Communication Technologies for Vehicles pdf pdf
Teks penuh
Gambar
Garis besar
Dokumen terkait
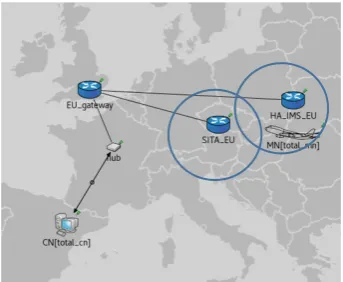
The system design uses Mobile Internet Protocol version 6 (MIPv6) combined with rapidly deployable network based on Mobile Ad- hoc Network (MANET) and IEEE 802.11
On JUMO process instruments with an RS422 serial interface, in addition to the four signal lines, the signal ground is always brought out to the connection terminals..
Figure 5 The effect of the number of nodes on the network efficiency of the proposed MAC protocol with Round Robin data sent every 8 hours and a
To evaluate the performance of the DSE-CMA equalization algorithm in the application of multime- dia data, a test image is transmitted over various wireless communication
In a typical scenario, you have a cable modem or DSL connection to the Internet, and you want to connect one or more laptops with wireless network cards to access the Internet
The only disadvantage of Boot Camp is that you lose access to all your normal Mac apps while you’re running Windows, which means that you have to shut down Windows and boot back
In the IP Settings dialog box, select the appropriate radio button for whether your wireless network card needs to obtain its IP addressing information from the access point ( DHCP,