Big Data : Securing the Data
Teks penuh
Gambar
Dokumen terkait
This is a very dif fi cult question as the notion of quality is very hard to describe in the fi rst place and secondly because the roles of allocation between a conceptual frame-
Data analysis that combines data from a variety of sources is starting to be applied within the financial sector, with unstructured data being increasingly used for
We have proposed Finding Structured and Unstructured features to improve a complex questions, and the preliminary work give a pretty good result, can
(1) the designed system enables the communication among different platform and datasets, including smart phones, web, and desktop application whether it is structured, semi-
Structured jihad is a congregation (DI, TII, Jama'ah Islamiyah), while the unstructured is like Nurdin M. Admitting that he was part of unstructured/disorganized one,
strongly universally consistent , given that the Bayes optimal rule for classi fi cation is known [20, 22]; (2) the misclassi fi cation rates using the DAMIP method are consis-
Although a lot of the metadata collected by Netflix – which actors a viewer likes to watch and what time of day they watch films or TV – is simple, easily quantified structured
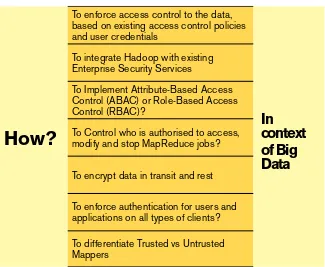
‘Big data’ refers to large and unstructured datasets characterised by six main components known as the six Vs: volume, velocity, variety, veracity, validity, and volatility.502 These