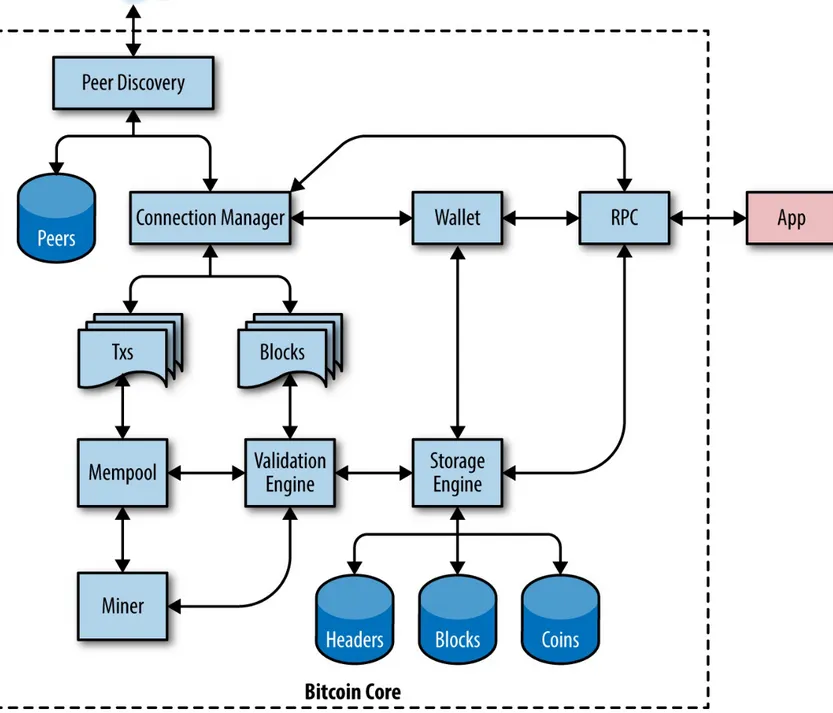
Mastering Bitcoin Programming the Open Blockchain (2017) pdf
Teks penuh
Gambar
Dokumen terkait
Based on the above test results can be concluded that: (1) Information technology experts assess the authentic assessment tools K13 base on ICT is in
Adapun hal yang menjadi alasan untuk melakukan penelitian efektivitas pendekatan cognitive behavioral therapy dengan setting kelompok untuk meningkatkan motivasi
Pada awalnya Instagram sendiri berkembang dari aplikasi iPhone untuk berbagi foto hingga sekarang menjadi sebuah perusahaan sosial internet yang berkembang.. iPhone
Along with the conclusions, propose the following suggestions: (1) the school management should monitor the performance of teachers through classroom
Telah dikembangkan model bahan ajar, yang karakteristiknya, didasari pada karak- teristik pelajaran fisika sesuai dengan tuntutan kurikulum 2013 dari sisi konten,
Perilaku kepala sekolah yang mampu memprakarsai pemikiran baru dalam proses interaksi dilingkungan sekolah dengan melakukan tujuan, prosedur, input, proses dan
Data yang digunakan dalam penelitian ini adalah data sekunder dari perusahaan di Indonesia yang melakukan proses akuisisi selama periode 2009- 2012 meliputi
Bedasarkan latar belakang masalah yang telah diuraikan sebelumnya, maka perumusan masalah dalam penelitian ini adalah “Bagaimana sikap masyarakat Surabaya terhadap